D365+
Business Applications
Manage your business processes more efficiently, increase productivity, and promote collaboration between departments.
NETEYE
IT Systems Management
Holistically and automatically monitor and manage your entire IT environment to get everything under control in less time.
Project Management Solutions &
Service Management
Improve the efficiency, reliability and quality of IT services with a solution that satisfies both users and customers!
SEC4U
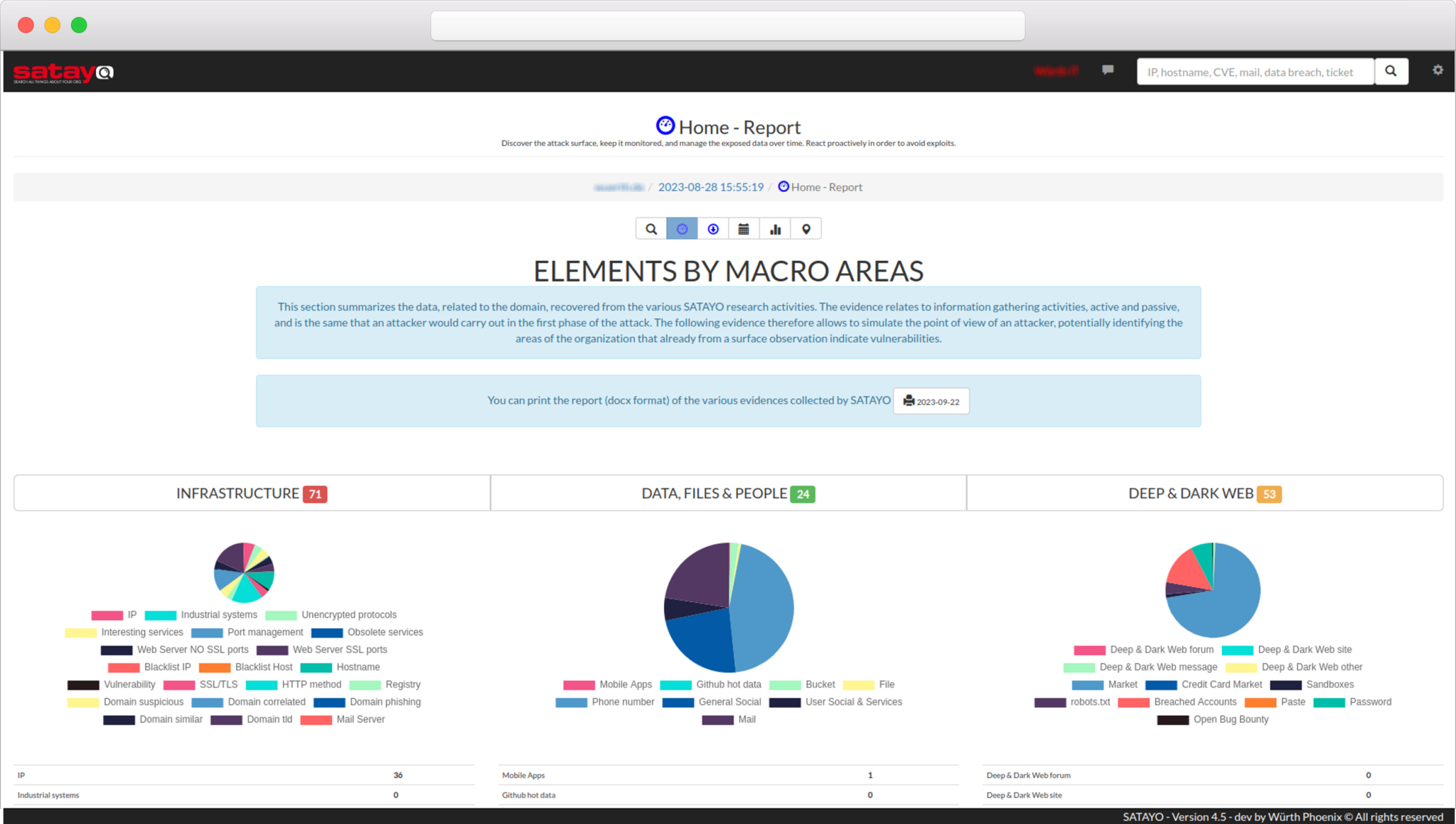
Cyber Security
Protect corporate data from external threats by exploiting the defensive and offensive point of view of security experts.
Sectors
We are committed to supporting various industries by providing essential IT solutions to foster business growth through automation and digitisation of processes.
Do you want to increase your skills?
Academy
Discover the courses dedicated to deepening your knowledge of the various NetEye modules, IT security, training new IT administrators, and the Dynamics 365 platform.








 One Time: A SATAYO scan available for a couple of weeks during which you can independently access the platform to verify the collected evidence.
One Time: A SATAYO scan available for a couple of weeks during which you can independently access the platform to verify the collected evidence.